On-Chain Privacy: From "Optional" to "Indispensable"
Author: ChainUp Investment
1. Introduction
In 2025, on-chain privacy experienced a major re-pricing event. Notably, driven by a resurgence of privacy awareness within the industry and significant advances in cryptographic technology, Zcash achieved substantial price discovery. These technological advancements include zero-knowledge proofs (ZKPs), multi-party computation (MPC), trusted execution environments (TEE), and fully homomorphic encryption (FHE).
- ZKPs: A method of proving the validity of a statement without revealing any information beyond its validity, enabling users to publicly share proofs of knowledge or ownership without disclosing details.
- MPC: A cryptographic protocol where multiple parties jointly compute data by splitting it into “secret shares,” with no single party able to see the complete data.
- TEE: A hardware-based solution. It is a secure “black box” inside the processor used to isolate data during processing.
- FHE: An encryption scheme that allows direct computation on encrypted data without decrypting.
The market has shifted from “anonymity” to “confidentiality,” which is a necessary functional feature in transparent blockchains.

In Q4 2025, interest in on-chain privacy surged, source: Dexu
1.1. Privacy Paradox
The history of privacy-focused cryptocurrencies dates back to 2012 when Bytecoin launched CryptoNote, which introduced ring signatures later adopted by Monero in 2014. In short, privacy in cryptocurrencies is not a new concept, but in early cycles, privacy coins were largely driven by ideological pursuits or evasion tactics, also serving as channels for bad actors to escape surveillance. The on-chain privacy dilemma in previous years can be attributed to three main factors: immature technology, fragmented liquidity, and regulatory hostility.
Historically, cryptographic technologies faced issues of high latency and cost inefficiency. Today, developer tools like Cairo (zkDSLs) and back-end frameworks like Halo2 have surged, enabling mainstream developers to utilize ZKPs. The trend of building zkVMs (zero-knowledge virtual machines) on standard instruction sets like RISC-V is making these technologies scalable and composable across various applications. MPC is no longer just for splitting private keys; with MP-SPDZ, it supports arithmetic circuits (addition/multiplication) and Boolean circuits (XOR/AND), enabling general-purpose computation. GPU advancements—such as H100 and Blackwell B200—support confidential computing, allowing AI models to run within TEE. The biggest bottleneck of FHE, bootstrapping latency (the time to “refresh” noise in encrypted computations), has decreased from about 50 milliseconds in 2021 to less than 1 millisecond in 2025, enabling real-time deployment of FHE encrypted smart contracts.
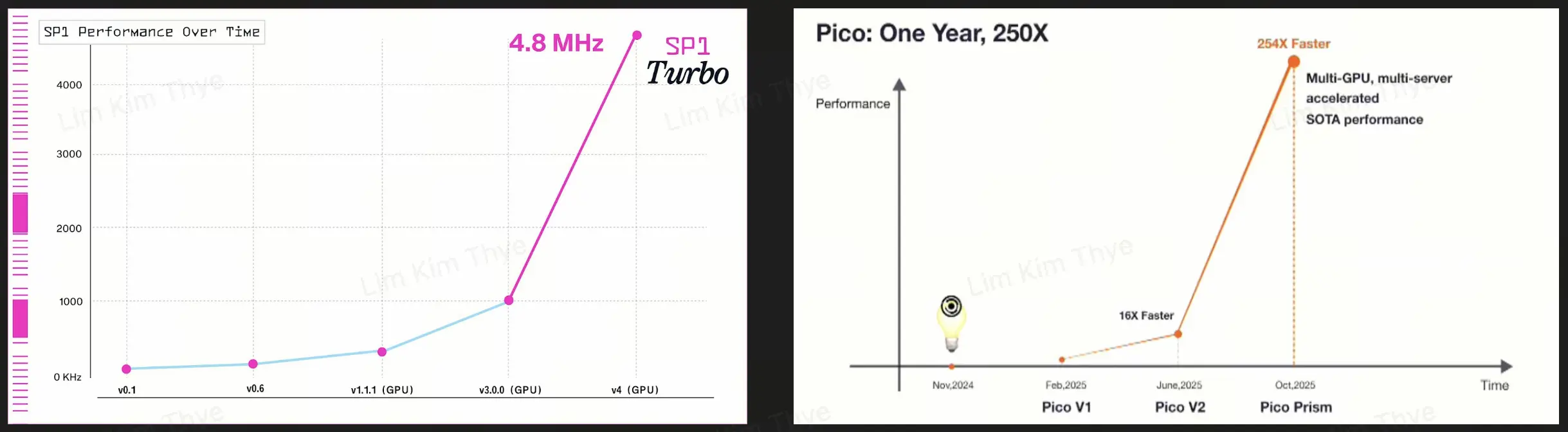
Iterative improvements in zkVMs and performance, source: Succinct, Brevis
Moreover, privacy is often isolated within specific blockchains, forcing users to leave active ecosystems across chains to achieve anonymity, which incurs high transaction fees and opportunity costs. Now, protocols like Railgun can directly integrate with DeFi applications, providing privacy as a shield against front-running and MEV extraction. Protocols such as Boundless, Succinct, Brevis, and similar services offer ZKP-as-a-Service, while Arcium and Nillion help build privacy-preserving applications using MPC, and Phala and iExec perform computations on application data within TEE without leaving their respective blockchains. Finally, Zama and Octra enable native FHE computations within applications.
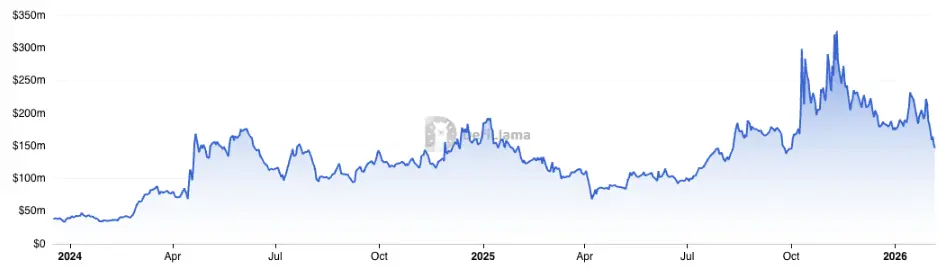
Railgun TVL, source: DefiLlama
Initially, blockchains required transparency to gain legitimacy. True builders had to distance themselves from hackers, money launderers, and other bad actors. In this environment, privacy features quickly became tools for dishonest participants. Projects like Tornado Cash, while favored by privacy-conscious users, placed those users at risk of funds mixing with illicit activities, making it difficult to prove innocence. This led to regulatory crackdowns: exchanges froze funds from mixers and delisted suspicious privacy tokens to pursue licensing. Venture capital and institutional funds avoided holding such assets due to compliance concerns. On-chain privacy became associated with “criminal” functions. Today, sanctions on Tornado Cash have been lifted. The industry has coalesced around the concept of “compliant privacy”, designing “viewable data” that allows users to decrypt their own transaction sources by providing “view keys” to auditors or regulators. This approach is visible in both Tornado Cash and Zcash.
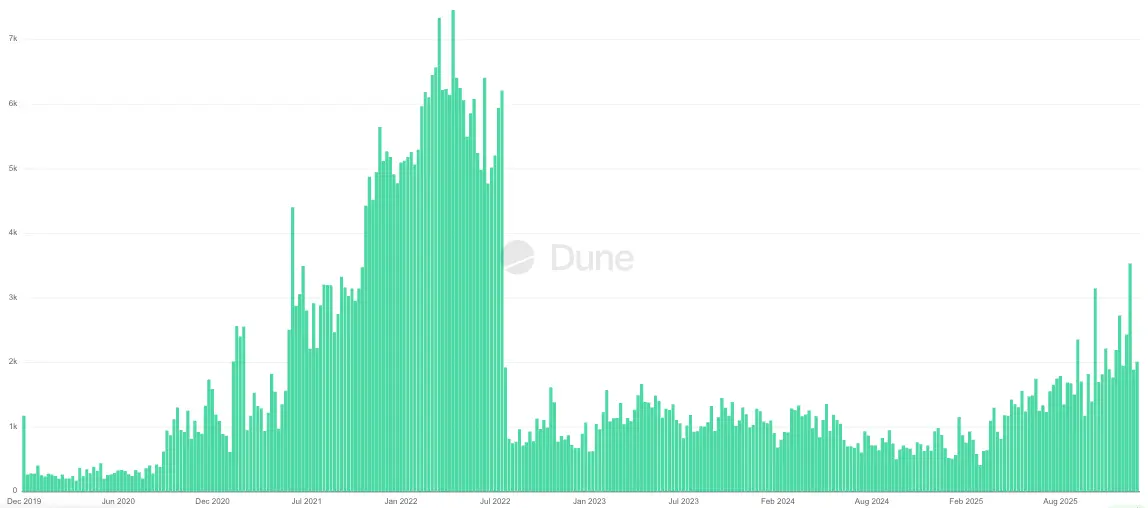
Major impact of sanctions on Tornado Cash fund flows, source: Dune
2. Current Privacy Technology Use Cases
Early setbacks do not mean privacy is unimportant. Ask yourself: “Do you want your actions of buying coffee today to expose your entire 10-year investment history?” Most would say no, but that is exactly what current blockchain setups do. As crypto legislation advances and more institutions participate, these new players are re-evaluating this issue. Fortunately, in 2025, the adoption of privacy tech is more driven by functionality than ideology.
2.1. Shielded Transactions
Using “viewable data” design, Zcash’s shielded transaction volume increased from 12% at the start of 2025 to approximately 29% now. The rising demand is driven by multiple factors, such as increased speculative interest in ZEC tokens and the natural desire to shield transactions from the public. The mechanism behind shielded transactions is called Commitment-Nullifier Scheme: senders can deposit shielded funds into a pool, with the network verifying the deposit using ZKPs to prevent double-spending, and creating a new shielded wallet for the recipient.
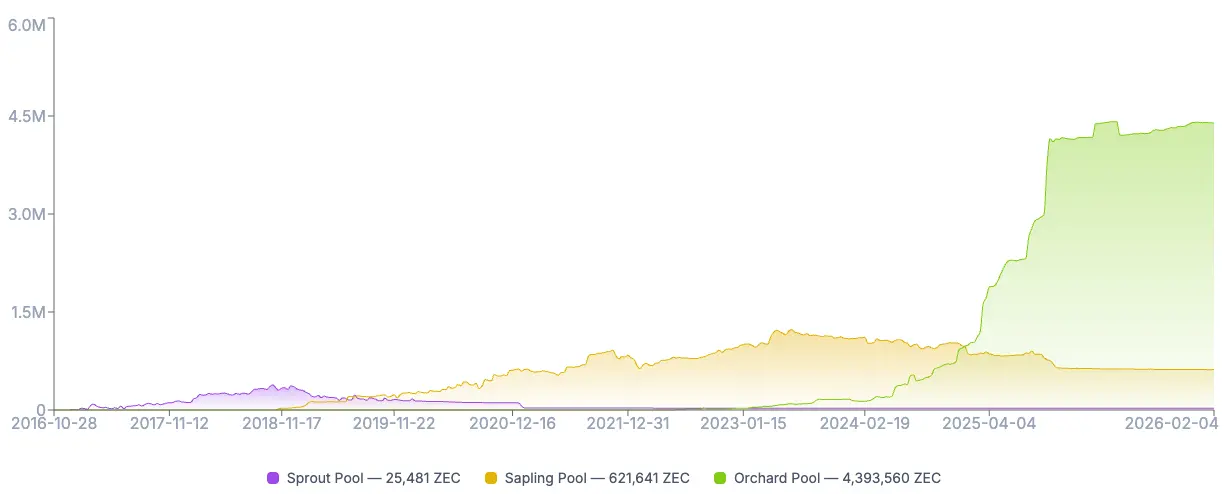
Growth of shielded ZEC supply on Zcash, source: ZecHub
One of the fastest-growing areas is crypto-neobanks, actively exploring privacy transactions for their users, such as Fuse, Avici, and Privily. These protocols employ different methods to obscure on-chain transactions.
2.2. High-Performance Execution Environments
Based on total value locked (TVL), ZK-2 layer networks grew by 20% in 2025, offering significantly cheaper execution environments compared to Ethereum Layer 1. These Layer 2s bundle all transactions into a small data blob, send it to a sequencer, generate proofs, and submit them to the base layer for verification.
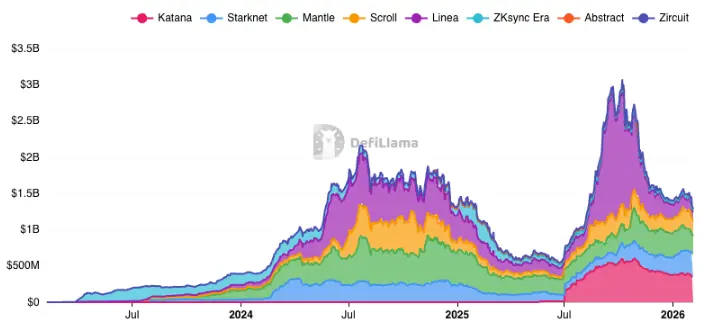
Application trends of major ZK-2 layer networks: TVL changes, source: DefiLlama
Today, ZK- provides comprehensive built-in privacy features, such as privacy smart contracts on Aztec and ZKsync Interop, which unify liquidity between ZK chains and Ethereum.
2.3. MEV Protection
One of the most common “hidden” use cases for privacy is Maximal Extractable Value (MEV) prevention. The transparency of blockchains allows front-running bots to see transactions in the mempool before confirmation and perform sandwich or other front-running strategies for profit. Flashbot SUAVE decentralizes block construction by encrypting the mempool, keeping transactions encrypted until the block builder commits to including them. Unichain also offers TEE-based block construction to prevent front-running on Layer 2.

Percentage of transactions protected by Flashbot Protect, source: Dune
2.4. Other Use Cases
Beyond the main use cases, developers are actively exploring on-chain privacy implementations to optimize applications and improve user experience.
-
Order Books: Whales like James Wynn and Machi Big Brother often face liquidation hunting. While Hyperliquid’s founders believe transparency fosters fair competition among market makers and tight spreads, large traders face risks of front-running or adverse trades. This creates opportunities for Aster, which offers hidden orders and plans to launch new shielded modes (Shield Mode) by 2026.
-
Identity: Certain activities, such as new bank account applications and ICOs, require identity verification. Protocols like idOS allow users to upload KYC once and reuse it across compliant protocols, zkPass helps generate Web2 credentials without revealing details, World ID proves personhood via iris hash, and ZKPassport verifies identity without leaving data on the user’s device.
- SEC Chair Paul Atkins stated that many ICOs should not be considered securities and thus fall outside SEC jurisdiction. His stance may lead to increased ICO fundraising and a higher demand for crypto KYC in the near future.
-
Cross-Chain Bridges: Historically, cross-chain bridges have been vulnerable, with Ronin Bridge and Multichain being hacked for $624 million and $126 million respectively due to private key leaks. ZK-cross-chain bridges minimize trust assumptions; once proofs are generated and verified, they provide immediate certainty, and as transaction volume grows, they become more cost-effective. Polyhedra Network connects over 30 chains via zkBridge and can be integrated as “DVN” into LayerZero V2 stack.
-
AI: ZK can help verify outputs generated based on expected inputs and processed by specific models. Giza enables non-custodial agents to execute complex DeFi strategies based on verified outputs. Phala uses Intel SGX enclaves to securely store private keys and sensitive data within AI agents.
3. Core DeCC Ecosystem Classification
On-chain privacy generally refers to Decentralized Confidential Computing Networks (DeCC). Although the market tends to classify protocols based on underlying privacy tech, each privacy stack involves trade-offs, and increasingly, protocols adopt hybrid approaches. Therefore, it’s best to categorize them as privacy blockchains, privacy middleware, and privacy applications.
Core DeCC Ecosystem Classification
3.1. Privacy Blockchains
The “privacy blockchain” category includes layer-1 and layer-2 networks where privacy mechanisms are embedded into consensus or execution environments. The main challenge for these networks is “cross-chain barriers”. They must attract users and liquidity from established chains; without killer apps making migration economically viable, this is very difficult. Privacy layer tokens are often allocated a “layer-1 network premium,” used as security collateral and gas tokens.
3.1.1. Legacy and Evolution of Layer-1 Privacy
Zcash has long been positioned as a Bitcoin-like chain with privacy features. It has a dual-address system allowing users to switch between transparent and shielded transactions, with “view keys” to decrypt details for compliance.
The protocol is transitioning from Proof-of-Work (PoW) consensus to a Crosslink hybrid model, which will incorporate Proof-of-Stake (PoS) elements by 2026, providing faster certainty than Nakamoto consensus. After the 2024 halving, the next halving is expected around November 2028.
Meanwhile, Monero maintains its default privacy approach using ring signatures, stealth addresses, and RingCT, making every transaction private. This design choice has led most exchanges to delist XMR in 2024. Monero also experienced several Qubic-based hashpower attacks in 2025, causing chain reorganizations of up to 18 blocks and about 118 confirmed transactions being reverted.
Secret Network is a TEE-based privacy layer built on Cosmos SDK since 2020, with view keys for access control. It positions itself as both an independent chain and provides TEE-as-a-Service for EVM and IBC chains. The team also explores confidential computing in AI and integrating threshold FHE into the network.
Canton Network, supported by Goldman Sachs, JP Morgan, Citi Ventures, Blackstone, BNY Mellon, Nasdaq, and S&P Global, is a layer-1 chain designed to introduce trillions of dollars in RWA (real-world assets) via a unique privacy feature called Daml Ledger Model. Parties connected to their subnet can only see a subset of the ledger, enabling verification only among participants, with outsiders unaware of the transaction’s existence.
Aleo is a ZK layer-1 network using a proprietary Rust-based language Leo, compiling code into ZK circuits. Users generate (or pay miners to generate) proofs off-chain, then only submit encrypted proofs to the network.
Inco positions itself as a FHE layer-1 network, providing FHE-as-a-Service across chains via cross-chain bridges and messaging protocols. This enables deep liquidity without building a DeFi ecosystem from scratch.
Octra is a high-performance FHE layer-1 network, developing its own cryptography called Hypergraph FHE (HFHE), allowing parallel processing during computation, achieving a peak throughput of 17,000 TPS on its testnet.
Mind Network leverages EigenLayer-like re-staking protocols to secure FHE validators. It aims to create an end-to-end encrypted internet (HTTPZ) and enable AI agents to process encrypted data.
3.1.2. The ZK-Layer-2 Networks
ZKsync has evolved from simple scaling to implementing comprehensive solutions like Prividium, ZKsync Interop, and Airbender. Prividium enables private transactions for companies while still settling securely on Ethereum. Airbender is a high-performance RISC-V zkVM prover capable of generating ZK proofs in sub-second time. ZKsync Interop allows users to provide collateral on ZK chains and borrow assets on Ethereum.
Starknet uses STARKs (Scalable Transparent ARguments of Knowledge) for high throughput scaling and features native account abstraction. Each account on Starknet is a smart contract, enabling invisible transactions via account contracts. The team also proposes a Layer-2 settlement on Zcash called Ztarknet, introducing a smart contract platform with Zcash’s privacy.
Aztec operates as a native privacy Layer-2 on Ethereum, using a UTXO-like note system for encrypted data and an account-based system for public data. It relies on Noir-based architecture with client-side proofs or PXE (Privacy Execution Environment), where users generate ZK proofs locally and submit them to the network.
Midnight, a partner chain of Cardano, uses Cardano’s SPOs for security while running its own execution layer. It is a TypeScript-based ZK layer-1 with selective disclosure features. It stakes ADA for security, uses unshielded NIGHT tokens for governance and gas (DUST), and defaults to shielded DUST as the gas token.
Phala depends on Intel SGX TEEs to protect privacy. It has shifted toward an AI co-processing model, allowing AI agents to run within TEEs, managing private keys and sensitive data, collaborating with Succinct and Conduit to migrate from Polkadot parachains to Ethereum Layer-2.
Fhenix is the first FHE EVM Layer-2 on Ethereum, bringing encrypted computation into the ecosystem. Transactions on this chain are protected from MEV because inputs are encrypted in mempool.
3.2. Privacy “Middleware”
“Privacy middleware” protocols operate on a Proofs-as-a-Service (PaaS) model, providing computation for proof generation, encryption, or verification. This space is highly competitive in latency, cost efficiency, and network support.
Boundless is a general-purpose ZK compute layer incubated by RISC Zero, functioning as a decentralized ZK proof marketplace. It allows any blockchain or application to outsource proof-heavy computations to Boundless.
Succinct Labs is a direct competitor to Boundless, positioning itself as a high-performance proof network. It adds dedicated circuits for common tasks like hashing and signatures to its zkVM (SP1), making proof generation faster and cheaper.
Brevis acts as a ZK co-processor, enabling smart contracts to query historical blockchain data trustlessly. Now, Brevis extends to Pico for general zkVM, precompiling heavy workloads and integrating as a dedicated circuit.
Arcium offers a configurable MPC solution for any chain, despite using Solana for staking, penalties, and node coordination.
Nillion provides high-performance MPC services for applications. Its Nil Message Compute (NMC) and Nil Confidential Compute (nilCC) enable data sharding to be computed without message passing, maintaining security within TEEs.
iExec RLC has been a long-standing DePIN protocol since 2017, providing cloud compute resources. It now emphasizes TEE-based confidential computing, enabling AI model training or inference without revealing data inputs, supporting chains like Ethereum and Arbitrum.
Marlin has pivoted from a blockchain CDN to a confidential compute layer (Oyster) and built a ZKP marketplace (Kalypso) on top of its compute layer.
Zama is a leading FHE protocol building fhEVM, TFHE-rs, and Concrete, used by protocols like Fhenix and Inco. Zama also offers FHE-as-a-Service on existing public blockchains and plans to integrate FHE into zkVMs after acquiring Kakarot.
Cysic develops hardware (ASICs) to accelerate ZKP generation, reducing proof time from minutes to milliseconds. Users can request proof generation from ZK Air (consumer-grade) or ZK Pro (industrial-grade ASICs).
3.3. Privacy Applications
This is the largest category within privacy blockchains and middleware, with only a small subset listed here. These protocols leverage ZK, MPC, TEE, or MPC to enhance user experience. Successful applications abstract away privacy complexities and deliver truly market-fit solutions.
Tornado Cash was the original decentralized, immutable mixer. It was sanctioned by the U.S. Treasury in 2022 but had sanctions lifted in early 2025. Nonetheless, it remains a high-risk tool for compliant entities.
Railgun has gained recognition from Vitalik Buterin. By integrating users’ “vaults” with DeFi protocols like Uniswap or Aave, it offers voluntary shielded transactions beyond Tornado Cash. Its shielded assets are about 20% of Tornado Cash’s, but it is widely seen as a potential competitor.
World (formerly Worldcoin) uses iris scans to establish “personhood proofs,” with biometric data encrypted and only ZKPs sent to the network. World ID is an effective tool for distinguishing humans from AI.
zkPass uses third-party TLS handshakes to generate proofs of personal identity and media data, enabling access to gated apps without revealing private info.
Privy allows users to log into dApps seamlessly via email or Web2 accounts, creating MPC wallets with keys split between user devices and secure servers. This eliminates cumbersome mnemonic backups and greatly improves UX.
Aster, in partnership with Brevis, plans to add privacy transaction features on its current hidden order book. The roadmap indicates Aster Chain aims to launch in Q1 2026.
Malda is a unified liquidity lending protocol that uses Boundless proofs to manage user lending positions across multiple chains.
Hibachi offers high-frequency decentralized perpetual trading, using Succinct proofs to verify off-chain CLOB orders on-chain.
Giza integrates machine learning into smart contracts, enabling them to execute complex DeFi strategies based on verified AI outputs. This allows AI-driven DeFi to operate on-chain without manipulation.
Sentient is an AI-focused Layer-1 network (supported by Polygon CDK), aiming to create an open AGI platform with contributor rewards. AI model owners upload models, which are encrypted and fingerprinted to verify outputs. It also builds the Sentient Enclaves Framework, utilizing AWS Nitro Enclaves for confidential AI model computation, shielding prompts and internal states from nodes.
4. Current Trends and Future Outlook
4.1.1. Rise of Privacy Middleware
We are witnessing a shift from monolithic privacy chains to modular privacy layers. Protocols can deploy on any existing chain (like Ethereum or Solana) and access privacy services via smart contracts, significantly lowering barriers to entry. As demand for privacy features grows and awareness increases, privacy middleware benefits as many startups find running their own compute-heavy confidential frameworks economically unfeasible.
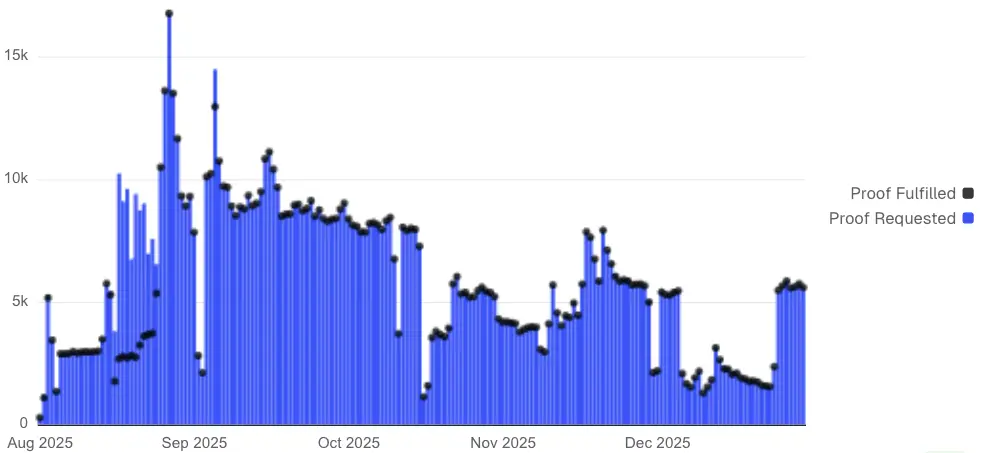
Requests and completions proof count on Succinct, source: Dune
4.1.2. Hybrid Solutions
Current privacy-enhancing tech has limitations: ZKPs cannot compute on encrypted data, MPC can suffer from latency issues with many participants, TEEs are vulnerable to fault injection and side-channel attacks (especially with physical hardware access), and FHE involves longer computation times with accumulated noise risking data corruption. Consequently, many protocols favor hybrid approaches or specialized hardware to optimize performance.
4.1.3. Confidential and Verifiable AI
Morgan Stanley estimates global AI-related capital expenditure at $30 trillion. As AI demand expands toward 2026, confidential and verifiable AI becomes a major trend in 2025, with scaling expected in 2026. Confidential model training on sensitive data like healthcare and finance records could mark another milestone in decentralized AI.
5. Summary
The era of privacy tokens without “view keys” may be ending. The industry bets that “selective disclosure” approaches will be accepted as a reasonable compromise. If regulators later reject this method, networks might be forced into “regulated permissioned chains” to maintain anonymity.
Maturity in privacy tech is key to unlocking trillions of dollars in traditional finance. Bonds, securities, and corporate payrolls cannot exist on transparent chains. As these protocols prove their robustness in 2025, the first major privacy RWA pilot projects are expected to launch on one of the networks mentioned earlier in 2026.
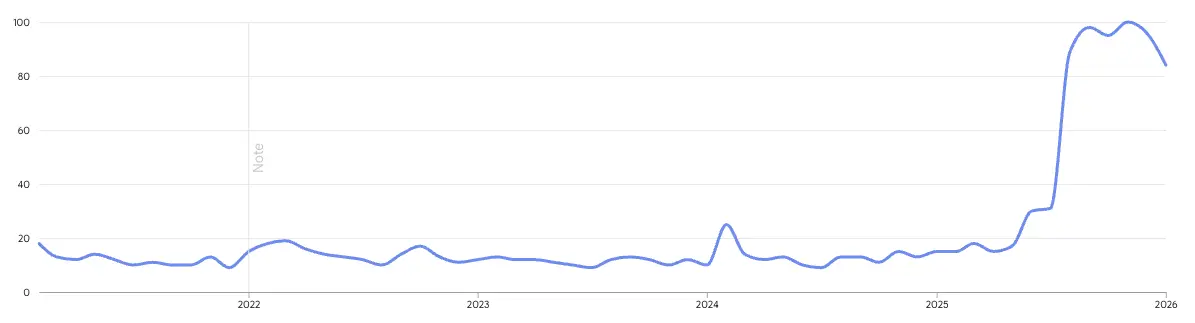
Google Trends over the past 5 years for “blockchain privacy,” source: Google
While interest in blockchain privacy may temporarily decline, application-layer demand for privacy features is expected to steadily grow, significantly improving user experience and attracting a broad non-crypto-native audience. This marks the moment when on-chain privacy shifts from “nice to have” to “essential.”