Trust Wallet Confirms Browser Extension Exploit: Over $6 Million Drained on Christmas
Trust Wallet has officially acknowledged a security vulnerability in version 2.68 of its Chrome browser extension, resulting in unauthorized withdrawals totaling more than $6 million from affected users on Christmas Day.
The company stressed that only this specific extension version was impacted, with the mobile app and other extension releases remaining secure.
(Sources: X)
Incident Details and Immediate Response
The breach was first flagged by on-chain investigator ZachXBT on December 25, who reported rapid fund drains across multiple Trust Wallet users shortly after a recent extension update.
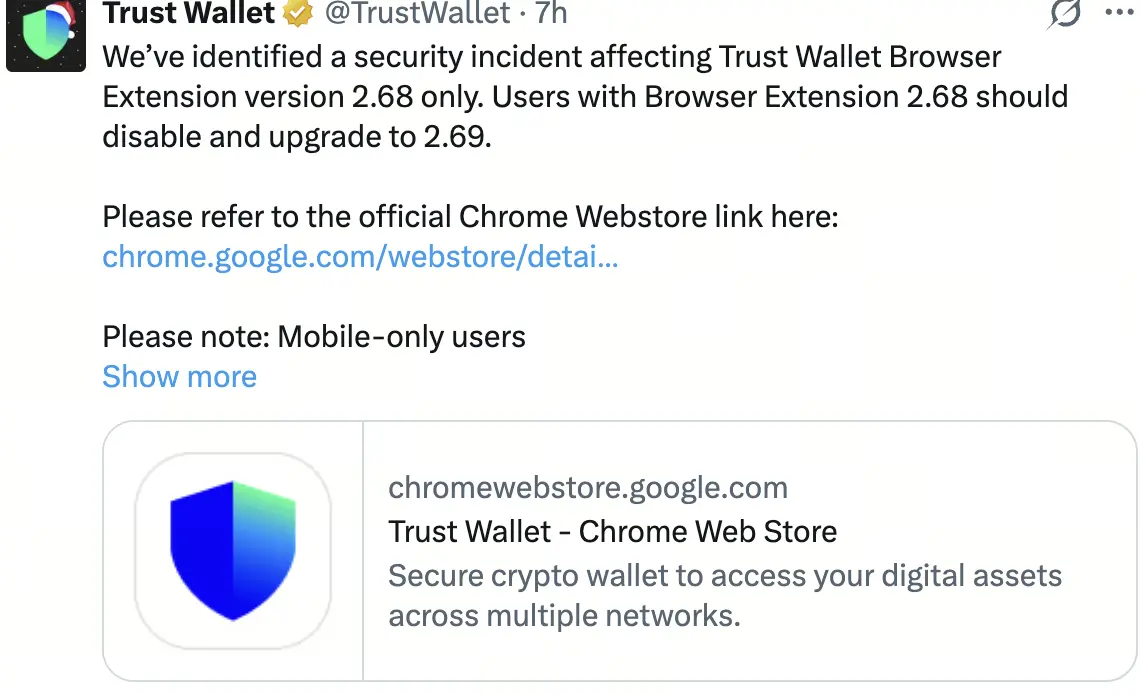
Trust Wallet quickly confirmed the issue on social media, urging users to immediately disable version 2.68 and upgrade to the latest release (version 2.69).
The team stated that an active investigation is underway, with further updates promised as details emerge. The exact technical root cause has not yet been disclosed.
ZachXBT’s analysis indicated attackers exploited the vulnerability to gain direct access to wallets, executing unauthorized transfers. Over $4 million of the stolen funds were reportedly moved to centralized exchanges, potentially via flash loans to obscure trails.
Hundreds of users appear to have been affected, marking one of the larger extension-related exploits in recent memory.
User Guidance and Security Recommendations
Trust Wallet issued clear safety steps:
- Disable and remove version 2.68 of the browser extension immediately.
- Upgrade to the patched version for continued use.
- Consider migrating assets to the mobile app, which offers biometric authentication and was unaffected.
- Monitor wallet activity closely for any suspicious transactions.
The company emphasized that the mobile application remains secure and recommended it as the preferred platform moving forward.
Broader Context and Historical Precedent
This incident echoes a prior Trust Wallet vulnerability in November 2022 involving WebAssembly code, which led to approximately $170,000 in losses. The firm fully reimbursed affected users at that time.
The current breach is significantly larger in scale, raising questions about potential compensation. As of December 26, 2025, Trust Wallet has not announced any reimbursement plans, though community pressure is mounting for clarity.
The event highlights ongoing risks associated with browser-based wallets, particularly vulnerabilities introduced through updates. It also underscores the sophistication of modern attackers targeting popular self-custody tools.
Implications for the Industry
The exploit serves as a stark reminder of the importance of timely updates, asset diversification across platforms, and vigilant transaction monitoring.
As non-custodial wallets grow in popularity, incidents like this are likely to intensify scrutiny on security practices across the sector—potentially accelerating calls for improved auditing, update protocols, and user education.
Trust Wallet continues to investigate and has committed to transparency as the situation develops. Users are advised to stay alert and follow official channels for the latest guidance.