How does idOS operate? A detailed breakdown of the complete workflow, from data storage to access approval
In traditional internet environments, user identity data is typically stored centrally by platforms, leading to issues like data silos, repeated verification, and privacy leaks. This is especially problematic in financial services, where users often need to complete KYC (Identity Verification) multiple times across different platforms. This not only reduces efficiency but also increases the risk of data misuse. With the growth of blockchain applications, this model has become a major bottleneck for Web3 user experience and compliance.
idOS was developed to address these challenges, serving as the “decentralized identity data layer” for Web3. By giving users control over their identity data and introducing encrypted storage with approval-based access, idOS enables secure, seamless sharing of identity information across multiple applications. This approach not only improves user experience but also provides foundational support for stablecoins, DeFi, and compliant financial applications.
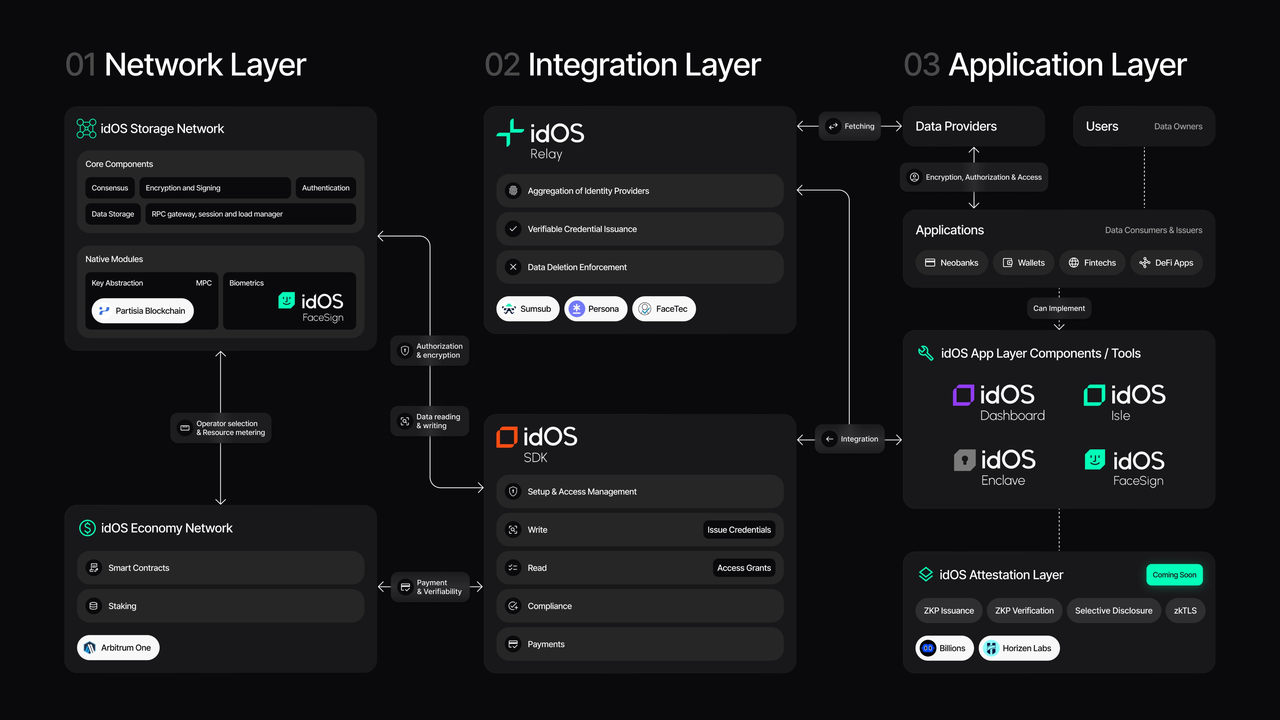
Core Logic of idOS: From Storage to Approval
idOS operates as a complete data lifecycle, encompassing five key stages: generation → storage → request → approval → use.
When a user accesses an application, they must first complete an identity verification process, typically handled by professional verification agencies (Issuers) such as KYC service providers. Once verified, the user’s identity data is encrypted and stored within the idOS decentralized network.
Unlike traditional databases, this data is not controlled by a single platform. Instead, it is distributed in encrypted form across network nodes. Users manage access permissions through their Private Key or identity credentials, enabling true self-custody of their data.
When another application (Consumer) needs to use this identity data, it cannot access the data directly—it must submit an access request. The request specifies the required data type and intended use, such as “verify if the user has completed KYC” or “confirm the user’s country.”
At this point, the core mechanism of idOS—Access Grant—comes into play. Users can approve or reject the request and decide on the scope of approval (for example, specific fields or time limits). Only after approval does the application receive the decrypted data or verification proof.
This process ensures that users always control their data, while enabling identity reuse across platforms.
idOS Data Storage: Encrypted and Distributed by Design
idOS combines encryption with a distributed architecture for data storage. Identity data is encrypted before being written to the network, ensuring that even at the node level, plaintext information is inaccessible.
Nodes in the storage network maintain data availability and security but cannot decrypt the data. This design safeguards privacy and eliminates the single-point-of-failure risk found in centralized storage.
Data is typically stored in a structured format—such as identity documentation, address information, or compliance status—enabling standardized integration across different applications. This structure provides the foundation for composable identity data.
Access Grant: idOS’s Core Approval Mechanism
Access Grant is one of idOS’s most critical features, defining how data is accessed and used.
All data access requires user approval, with granular control. Users can decide not only whether to approve access, but also:
-
Which data can be accessed
-
The time frame for access
-
Whether repeated use is permitted
This model acts as a “data permission layer,” separating data ownership from usage rights, enabling flexible privacy management.
For applications, this means they do not need to store sensitive user data; they simply request approval as needed. This significantly reduces data compliance risks.
Participants and Data Flow
The idOS network includes four main participants, forming a complete data flow system.
Users own and control their data, managing approvals and access permissions.
Issuers verify data, generating trusted identity information such as KYC or compliance checks.
Consumers use the data—such as trading platforms, stablecoin applications, or DeFi protocols—by requesting approval.
Node operators maintain network operations, ensuring data storage and availability.
The typical data flow: User → Issuer (verification) → Encrypted storage → Consumer request → User approval → Data use.
This process can be repeated across different applications, enabling identity data reuse throughout the ecosystem.
Example Workflow: KYC Reuse with idOS
idOS’s value is especially evident in KYC reuse.
Once a user completes identity verification on one platform, their data is stored in the idOS network. When accessing another platform that requires KYC, the user does not need to resubmit documentation—they simply authorize use of their existing data through idOS.
When the new platform submits a request and the user approves, the system returns the verification result or necessary information. This usually happens in the background, creating a “one-click verification” experience.
This approach reduces the cost and friction of repeated verification, while improving data consistency and compliance.
Key Differences: idOS vs. Traditional Identity Systems
The core difference between idOS and traditional centralized identity systems is in data control and access.
In traditional systems, platforms control user data, limiting user control. In idOS, users control their data, and access is only granted through approval.
Traditional systems also lack cross-platform reuse, while idOS enables identity portability through a unified data layer.
These differences make idOS well-suited for the collaborative, multi-application Web3 environment.
Summary
idOS uses encrypted storage and approval-based access to build a decentralized identity data network, empowering users to control their data and reuse it securely across applications. Its core strengths are reducing identity verification costs, enhancing privacy, and providing scalable identity infrastructure for stablecoins and on-chain finance.
FAQs
What is idOS Access Grant?
Access Grant is a data access approval mechanism that lets users control who can access their identity data and the scope of access. It is the foundation of data sovereignty in idOS.
Does idOS store users’ plaintext data?
No. All data is encrypted before being stored in the network. Nodes cannot access plaintext information; decryption or verification results are only provided after user approval.
How does idOS enable KYC reuse?
By encrypting and storing verified identity data in the network, users can authorize other platforms to use this data, avoiding repeated submissions.
How is idOS different from traditional databases?
Traditional databases are controlled by platforms, while idOS uses decentralized storage and user approvals, shifting data control from platforms to users.
Which applications use idOS?
idOS is primarily used in scenarios requiring identity verification, including stablecoin platforms, DeFi protocols, and compliant financial services.
Related Articles

In-depth Explanation of Yala: Building a Modular DeFi Yield Aggregator with $YU Stablecoin as a Medium

What is Stablecoin?

Blockchain Profitability & Issuance - Does It Matter?

Stripe’s $1.1 Billion Acquisition of Bridge.xyz: The Strategic Reasoning Behind the Industry’s Biggest Deal.
An Overview of BlackRock’s BUIDL Tokenized Fund Experiment: Structure, Progress, and Challenges